A Day at BSides Manchester
This was the first BSides event I’ve attened and it was a lot of fun.
I’ve heard people in the past say that it’s not what you directly learn at conferences but the discovering of things you weren’t aware of that you now know you must spend time looking at. This rang true for me at this conference.
I’m looking forward to seeing videos of the talks I missed (and re-watching some I attended), here’s my feedback on the talks I saw.
HTTP Invisibility Cloak (Soroush Dalili)
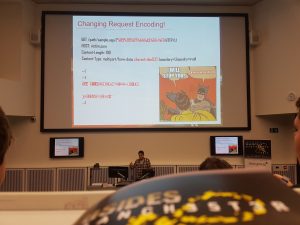 This was a replacement talk as the speaker who was meant to be talking was unable to make it on the day after falling unwell. I’d already seen this talk at SteelCon so was a little disappointed at first but Soroush had updated it since June and it turned out to be a cracker. Having time for what I’d heard last time to sink in may have helped but it was made so much more real when he was going through the various techniques he mentioned which WAFs each method worked against (and yes it included the big ones!). I look forward to trying some of these methods out when testing my own apps that sit behind a WAF.
This was a replacement talk as the speaker who was meant to be talking was unable to make it on the day after falling unwell. I’d already seen this talk at SteelCon so was a little disappointed at first but Soroush had updated it since June and it turned out to be a cracker. Having time for what I’d heard last time to sink in may have helped but it was made so much more real when he was going through the various techniques he mentioned which WAFs each method worked against (and yes it included the big ones!). I look forward to trying some of these methods out when testing my own apps that sit behind a WAF.
Cracking the lens: Targeting HTTP’s hidden attack surface
(James Kettle)
 James is head of research at Port Swagger (the guys who created Burp Suite), in his talk he showed how systems sitting behind proxies/load balancers etc can be sent malformed requests to get them to do things you wouldn’t normally have access to, for example returning a site or configuration settings intended for internal access only (SSRF). I really enjoyed his presentation and will watch it again when the video get released.
James is head of research at Port Swagger (the guys who created Burp Suite), in his talk he showed how systems sitting behind proxies/load balancers etc can be sent malformed requests to get them to do things you wouldn’t normally have access to, for example returning a site or configuration settings intended for internal access only (SSRF). I really enjoyed his presentation and will watch it again when the video get released.
Bypassing Email Gateways (Neil Lines)
I saw Neil present at Steelcon, he has quite an infectious style and makes everything clear and easy to follow. In this talk he showed how he was able to bypass email gateway scanners by embedding an old school batch file (containing obfuscated code to run a PowerShell command) into office documents via ole. Based on the results he concluded it looks like the email scanners are relying heavily on signatures to detect malicious content. Always like the way he shows some sneaky ways to make something that looks a little shady in Word/PowerPoint into something most users would click without a second thought.
Testing Docker Images Security (Jose Manuel Ortega)
 I use Docker on a daily basis in a development environment so thought this would be a great talk to attend. He went through some best practices on keeping the environment secure from setting appropriate user permissions to checking dependencies against vulnerability databases and making sure the checksums of images you’re pulling from the repository match what you are expecting. Great talk and went away knowing more than when it started, thank you Jose.
I use Docker on a daily basis in a development environment so thought this would be a great talk to attend. He went through some best practices on keeping the environment secure from setting appropriate user permissions to checking dependencies against vulnerability databases and making sure the checksums of images you’re pulling from the repository match what you are expecting. Great talk and went away knowing more than when it started, thank you Jose.
Red Teaming Workshop (Phil Lynch & Ben Turner)
 This was the part of the day I’d been looking forward to the most based on the workshops I’d attended at Steelcon earlier in the year, so to guarantee we wouldn’t miss out myself and a friend made sure we arrived early and started setting up the VMs provided.
This was the part of the day I’d been looking forward to the most based on the workshops I’d attended at Steelcon earlier in the year, so to guarantee we wouldn’t miss out myself and a friend made sure we arrived early and started setting up the VMs provided.
The aim of the workshop was to craft an email with a malicious attachment to gain a foothold on the virtual lab environment then to think about persistence, privilege escalation, lateral movement and exfiltration of data. I’ve read about the tools/techniques but the was the first time actually attempting to use them, this along with not knowing the network layout or if there were any IDS in place meant it was pretty exciting – that was until I started having a few problems with the networking of my virtual machines (not cool!).
I’d love to have another bash at it so I’m going to build my own virtual lab at home.
Random pictures from the trip

How the local cash machines looked before Leigh-Anne Galloway turned up.